Analyst on messenger flaws and AI scams

Experts describe increasingly complex social engineering and malware tactics targeting everyday smartphone users.
Fraudsters continue to deceive us successfully. While protection technologies are evolving, companies devise ever new ways to safeguard our data and spend billions on it, and authorities block calls in popular messengers — allegedly for safety. Nevertheless, the internet already knows everything about us, and keeping data safe is getting harder and harder.
So how do you avoid handing your money and information to scammers? Are Telegram and MAX dangerous? And what new schemes are attackers inventing to fool us? The 72.RU newsroom spoke about this with Dmitry Galov — head of Kaspersky Global Research and Analysis Team (GReAT) in Russia.
Dmitry Galov analyzes complex targeted attacks, researches malware for non-Windows platforms, and studies Internet of Things vulnerabilities. He investigated one of the most sophisticated spying campaigns against iOS users — «Operation Triangulation», which prompted Apple to close four critical vulnerabilities at once.
«The schemes are becoming more and more multilayered»
— Despite advances in technology, scam calls still show up regularly. Is it easier to steal data over a call or in a chat?
— «Easier or harder» isn’t really the right question here. Why? Because a single call or message from a scammer usually does not lead to the compromise of data. The schemes attackers use today are rarely one‑step.
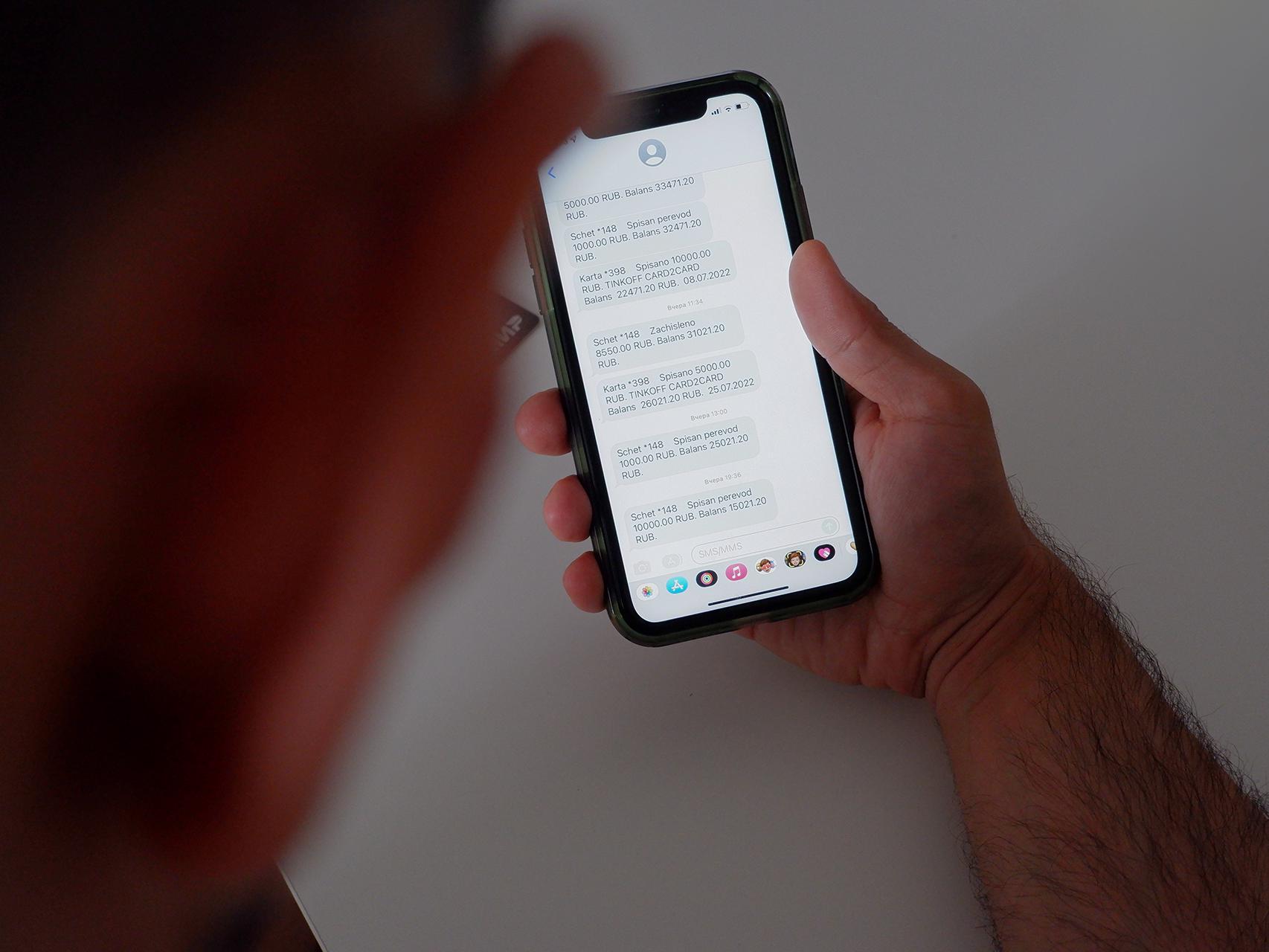
A simple SMS from scammers is unlikely to bring them success. So it is either a chain of calls or first a message in a messenger from one person and then a call from another. Attackers may call supposedly on behalf of law enforcement or pose as a security service that has prevented something. It might look like this: «Your account showed suspicious activity; install a free program so there are no problems in the future». And under the guise of a useful program, they send malware.
The schemes are becoming more and more multilayered; attackers craft convincing stories that, unfortunately, people may believe.

Interview outlines risks in messengers, including Android APK threats and NFC-enabled banking trojans.
— Wouldn’t it be simpler to just send a link by email or in a message?
— A call is indeed more labor‑intensive — attackers need an operator — whereas mass messaging in messengers can reach far more people. But attackers often use blasts to narrow the funnel down to those who didn’t ignore the fake message and didn’t check the number it came from — that is, to those who are more likely to believe the legend and fall for the trick.
— Tell us about ways to steal data in messengers.
— In messengers, attackers continue to use techniques previously seen in SMS and phishing emails. But the wide variety of possible storylines in messengers definitely gives them more freedom.
In particular, while an SMS is only text, in a messenger scammers can build a storyline and thus distribute not only text but also images, links, and infected files. For example, there was a scheme where scammers created a site for job seekers. If a person showed interest, a fake manager in a messenger sent them an apk file (APK is the file format used in the Android operating system to install apps) — presented as a program allegedly needed to perform work tasks. In reality, the attackers were distributing the Mamont mobile banking trojan.
— Speaking of APK: that’s an Android file. Does this mean iPhone users are safe because they have a different operating system?
— Yes, this remains a major cybersecurity issue for users: on Android you can install files from unknown — and often dangerous — sources, which you can’t do at scale on iOS. Theoretically this is possible on iPhone as well, but it is heavily restricted in many ways.
— And more about messengers. Calls are blocked in Telegram and WhatsApp, with the explanation that this protects against scammers. We now have the MAX messenger, whose security users also complain about. Is there any difference if the schemes seem the same? In both cases, anyone can message you, you click a link, and that’s that.
— Good question. The answer is this: when it comes to phone scams, in recent times they have actively shifted into messengers, which has made them harder to combat.

Why? Because the specifics of some services do not allow full‑fledged user‑protection projects to be implemented. For example, in WhatsApp (owned by Meta; its activities are designated extremist and banned in Russia) a caller can change the user name after each call, which can affect the process of determining call reputation.
One can say that users of many different messengers may encounter many different cyberthreats. It’s important to pay attention to what services do to protect their users. For instance, we recently reported that MAX implemented our solution for automatic number screening in the messenger.
Of course, no product can protect users 100%. But we believe that joining forces with different platforms and services will help fight digital fraudsters more effectively together.

Guidance includes caller ID tools, app restrictions, and raising digital literacy for seniors.
— In your view, why doesn’t Telegram work, say, with Kaspersky or any other company?
— I don’t know Telegram’s internal workings. Messengers themselves are also fighting scammers. There are messenger developers, banks, telecom operators, and security vendors — each with its own view of the problem. If we combine efforts, knowledge, and technologies, we can significantly increase the effectiveness of the fight against online and telephone fraud.
AI voice generation and other hackers’ innovations
— Is AI generation of a familiar person’s voice a reality? Can scammers steal my voice and call, for example, my parents?
— If scammers have only a recording of a couple of words, then hardly. The more original audio content attackers have, the more convincing the deepfake will be. But even then you shouldn’t fear that they will try to “steal” your voice in particular.
Today schemes are more common in which scammers generate the voice of, say, a company head and send voice messages in a messenger to employees on his behalf. Even more often, they use AI to generate a celebrity’s face or voice and, without consent, deploy it in ads for, for example, scam resources.
— What other novelties have attackers come up with?
— One trend this year is attacks on Android users using NFC trojans to steal people’s money. This cyberthreat first appeared in Europe because their financial security model works slightly differently. For example, they have cards without numbers that can only be used together with a device — to log in to online banking, you need to tap such a card to a smartphone.
Attackers began to use this technology: essentially, one infected device becomes a reader, and the second — the attackers’ device — a tapper that remotely receives stolen card data. In this way, scammers can pay for something or steal money.
At the end of 2024, attacks on Android users involving NFC trojans began to be recorded in Russia and have only been gaining momentum throughout the year.
— Do methods differ from region to region? Maybe Tyumen (Russia) has its own specifics?
— They do, but only slightly. Looking across regions, two elements change. First is the specifics of the organizations present in the region. Second is the regional context used to catch a potential victim’s attention — for example, if benefits are announced, funds allocated, promotions held, and so on. Overall, though, this is rare — in terms of techniques and tactics, things are fairly uniform and global.
The internet knows everything about you
— People now leave a huge digital footprint. What can be learned about a person from their data?
— Everything that ends up on the web potentially cannot be fully removed. You can either feel sad about it or simply be ready for the consequences. Often data appears online after actions taken by the user. A second, more abstract scenario is when data leaks from a third party. For example, when we check into a hotel, they scan passports. Potentially, if attackers compromise the hotel, they can gain access to that data. The same goes for sites where we register, and so on.
Do we have the option to avoid all this? You could try not using any digital services at all, not going on vacation. But I don’t think that option will suit anyone.
It follows that from the moment we give confidential data to a company, we as users cannot control its security. Because of a cyberattack or an insider, data can potentially leak.
If it ends up in attackers’ hands, users may face more convincing fraud schemes. Therefore, the main protection for users is improving digital literacy, staying informed, and using security solutions.
— How can you reduce your digital footprint?
— At a minimum, avoid oversharing — don’t post photos of your passports on social networks — basic things like that. Of course, secure your devices so attackers cannot infect them. Secure your accounts, because even if nothing is posted publicly, we are still people and we sometimes send things in messengers, social networks, and email.
— And the last question, which also worries everyone. How can you protect your older relatives from scammers?
— There is, of course, the kind answer: raise their cyber‑literacy; tell and explain. At the same time, it’s important to set up some technical protections and restrictions. For example, install a caller‑ID app that blocks spam numbers so suspicious calls are rejected automatically; set a self‑ban on loans; configure the phone to restrict installing apps from third‑party sources; and better yet, help install any necessary apps. In other words, you can physically reduce the number of situations in which a person might make a mistake because of attackers’ actions.
Earlier, we spoke about children’s cybersecurity with analyst Andrey Sidenko — how to protect a child from scammers, bullying, and sexualized violence. The interview is at this link.





