Moscow Law Enforcement Reveals Phone Hacking Tactics

Forensic experts demonstrate techniques for accessing locked mobile devices during a security conference event.
Our entire lives have long been stored in smartphones, and the police are well aware of this. When solving crimes, forensic experts always check gadgets, but extracting data from them isn«t always easy. We found out what law enforcement is capable of and whether cybercriminals can use their methods.
How Law Enforcement Gains Access to Devices
Issues of gadget hacking were discussed at the Moscow Forensics Day 2025 conference. Olga Tushkanova, head of the department at the Main Directorate of Forensics of the Investigative Committee (SK), said that law enforcement learns passwords for phones and computers through some «operational method.» She did not elaborate on the details.
A forensic expert can submit a petition to the investigator for the user to voluntarily provide the phone«s code or unlock it with their face. How to compel a person to do this was not specified.
«We have petitions, and the investigator can interrogate the person from whom the phone was seized. <…> The most interesting [petition] is for the user to be present during the examination to undergo biometric identification (most likely authentication, that is, unlocking. — Ed.),» said the SK representative.
She acknowledged that without unlocking the phone with a face, some actions with it are impossible.
Is It Legal to Demand Passwords?
Lawyer Georgy Krasnov reminded that citizens have the right not to give passwords to investigators and not to unlock smartphones using biometrics. The same applies to airport screenings, where passengers sometimes voluntarily provide access to their phones.
«There is no punishment for refusal. This is analogous to the right not to testify against oneself (Article 51 of the Constitution). There is no obligation to provide access; it»s enough to politely refuse and endure an angry glare,« he told MSK1.RU.
Moreover, in 2023, the Supreme Court prohibited considering a suspect«s refusal to provide a password as evidence of guilt.
Sometimes Russians describe how exactly law enforcement asks for access to their gadgets. For example, in February, law enforcement officers attended a letter-writing evening for prisoners in Yekaterinburg. Ivan Doronin, secretary of the Sverdlovsk branch of the Libertarian Party of Russia, then stated that those present were demanded to provide phone passwords, and later some discovered extra connections in Telegram.
Lawyer Georgy Krasnov told MSK1.RU that in such a situation, accessing the user«s account is only possible by knowing the password.
«If phones and passwords were provided to the officers, then it is not technically difficult to log into the account and export (download) all chats. It is impossible to do this remotely and without the code-password,» he explained.
Simple Protection Can Be Cracked in Seconds. Complex One Takes Years
When a suspect knows their rights and remains silent, their gadget is hacked through password guessing. For instance, Valeria Vakhrushina, an employee of MKO System, demonstratively cracked a weakly protected archive in just 11 seconds.
«I know that IT people always say: set proper passwords, make them multi-character, use different cases, special symbols, make them at least 10 characters long. Unfortunately, ordinary users typically don»t use this,« she said.
Vakhrushina listed the most popular passwords, which can be cracked in less than a second. These are simple combinations like 1234, admin, password. Russians like to use phone numbers, the name of the country, the president«s surname, the word »sniper,« and (surprisingly) baltika9.
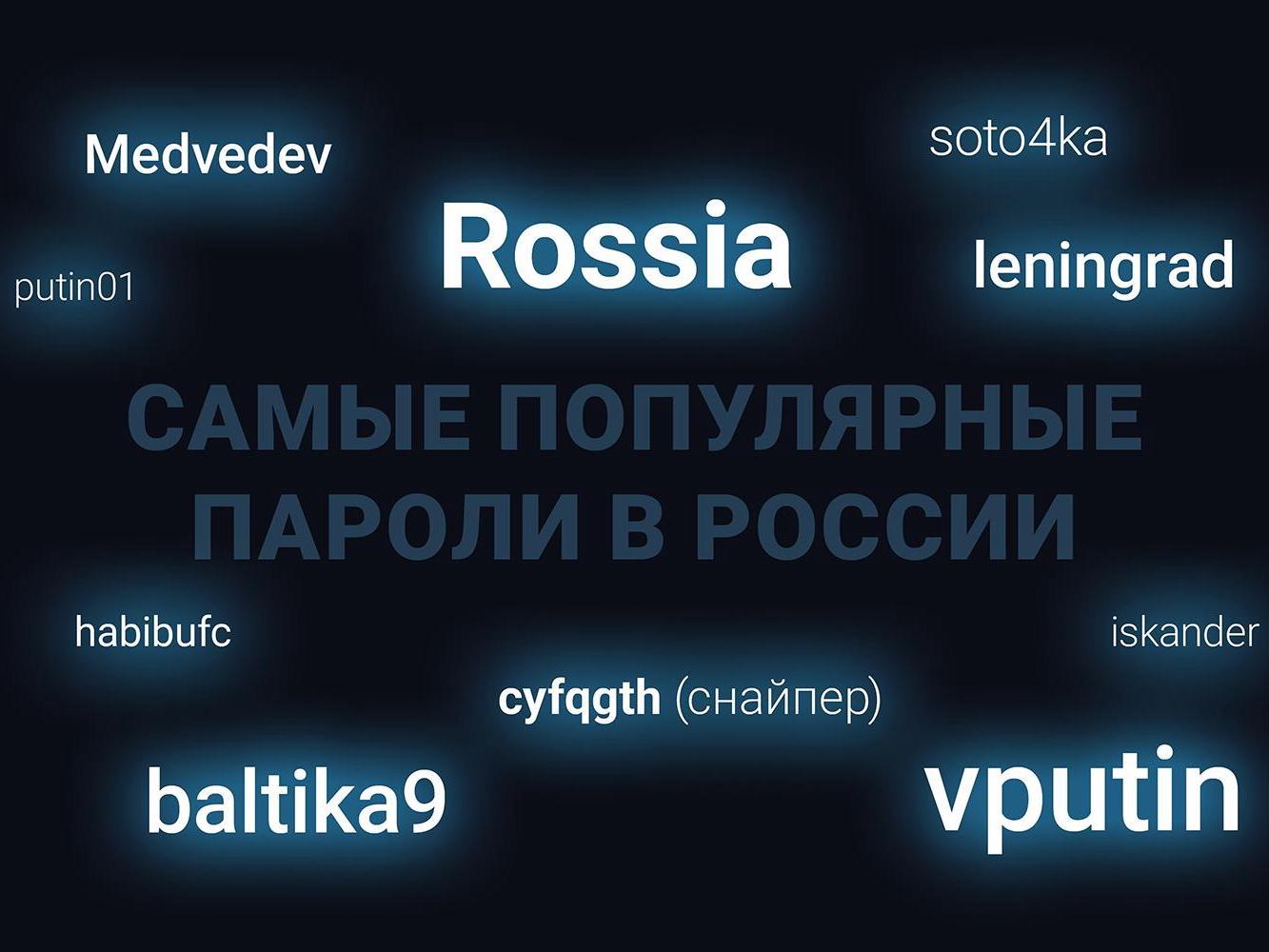
Common weak passwords used by Russians that can be cracked in seconds are listed by cybersecurity professionals.
Another speaker, Vyacheslav Chikin from ACELab, noted that zoomers actively use hearts and other special symbols in passwords. He admitted that forensic experts« capabilities are limited and gave an example of how he »struggled for a day« but still couldn»t figure out the eight-character password for a phone that his son had forgotten.
Can Scammers Learn Passwords in the Same Way?
Alexey Raevsky, CEO of cybersecurity developer Zecurion, told MSK1.RU that guessing the password for an account like Gosuslugi is difficult because the number of attempts is limited and the service will interrupt the operation.
«But if hackers manage to obtain a password database, they most likely won»t hack a specific account. Whoever has a simpler password will be hacked first, and it«s quite possible that the malicious actors will be satisfied with what they get,» the expert explained.
Alexey Raevsky advises assuming that scammers have the same capabilities as law enforcement. According to him, if something is possible, even if unlikely, one needs to protect against it.
«It»s clear that law enforcement officers are exceptionally honest and all follow the law, but there is still a human factor. And it«s possible that someone who doesn»t follow the rules will be found. Therefore, it«s better to assume that scammers can obtain the same information as law enforcement agencies,» said Raevsky.
Cybersecurity experts warn that fraudsters can use similar password-cracking methods as law enforcement agencies.
If we talk about the system for operational-search activities (SORM), scammers certainly don«t have it, the speaker added. He separately noted that the authorities take personal data leaks seriously.
«For example, there were so-called lookup services, they were used by everyone, but at some point they started being used for terrorist acts. And very quickly, all this was shut down,» recalled Raevsky. «Immediately, all these lookuppers were put on a list, a couple were imprisoned, the others hid. And that was the end of it.»
Alexey Moskvichev from MKO System spoke at the conference about how malicious actors steal money in the classic way – through deception. The expert reminded that applications should be installed from official stores, card codes should not be shared with anyone or entered on suspicious websites. If card data is stolen, it should be blocked immediately.
Can Forensic Experts Retrieve Deleted Data from Phones?
Vladimir Greshnov, a specialist from the development department of Eletek LLC, said that special «duplicators» can recover even deleted data. According to Alexey Raevsky, CEO of Zecurion, retrieving such files is indeed not difficult. When a file is deleted, it doesn«t disappear physically; just a »Deleted« flag is set in the system.
«If nothing has been overwritten in its place, then it can be pulled out from there. This was back in the era of personal computers, before any gadgets, and it worked fine. I think it works exactly the same now. And if it has already been overwritten, then, of course, the file cannot be recovered,» the expert explained to MSK1.RU.
Scammers regularly come up with new ways to deceive Russians. For details on how cybercriminals are caught, read our interview with Anton Kononenko, head of the MVD department for combating illegal use of information and communication technologies.





